Get completely ready for a facepalm: 90% of credit history card audience at the moment use the similar password.
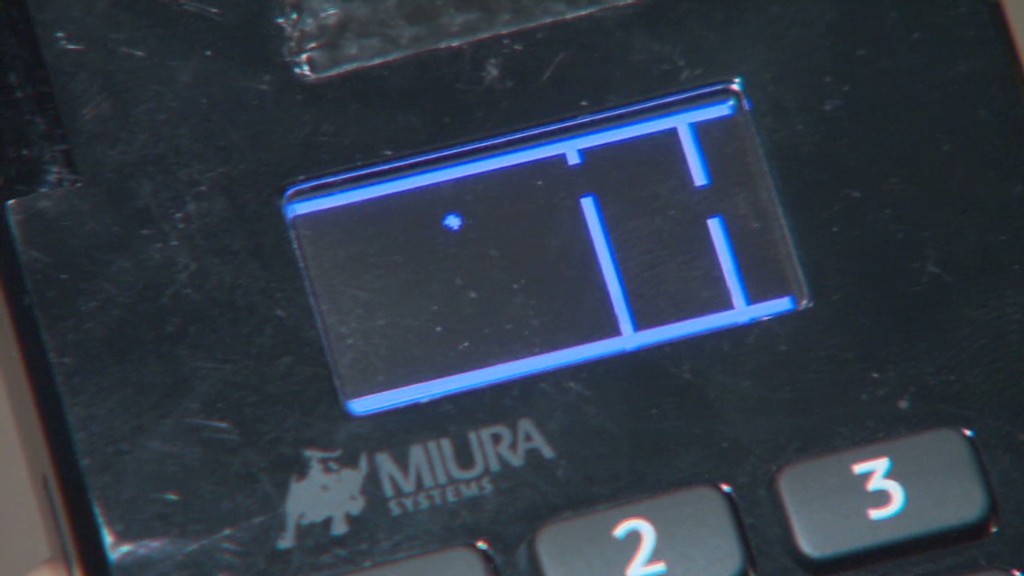
The passcode, set by default on credit rating card equipment given that 1990, is quickly discovered with a brief Google searach and has been exposed for so very long there’s no sense in striving to hide it. It can be either 166816 or Z66816, relying on the machine.
With that, an attacker can gain comprehensive command of a store’s credit card readers, potentially letting them to hack into the devices and steal customers’ payment data (feel the Goal (TGT) and Home Depot (Hd) hacks all around once more). No marvel huge stores maintain shedding your credit card knowledge to hackers. Stability is a joke.
This newest discovery arrives from scientists at Trustwave, a cybersecurity business.
Administrative obtain can be utilised to infect equipment with malware that steals credit card knowledge, spelled out Trustwave govt Charles Henderson. He detailed his findings at final week’s RSA cybersecurity convention in San Francisco at a presentation called “That Issue of Sale is a PoS.”
Get this CNN quiz — obtain out what hackers know about you
The difficulty stems from a sport of scorching potato. Product makers market equipment to distinctive distributors. These suppliers market them to suppliers. But no just one thinks it’s their position to update the master code, Henderson instructed CNNMoney.
“No 1 is changing the password when they established this up for the very first time most people thinks the safety of their level-of-sale is anyone else’s responsibility,” Henderson said. “We’re building it very easy for criminals.”
Trustwave examined the credit rating card terminals at a lot more than 120 vendors nationwide. That contains key clothes and electronics suppliers, as perfectly as community retail chains. No precise retailers ended up named.
The large bulk of devices were produced by Verifone (Pay out). But the exact difficulty is present for all important terminal makers, Trustwave reported.

A spokesman for Verifone said that a password alone is not ample to infect machines with malware. The business stated, until eventually now, it “has not witnessed any attacks on the protection of its terminals based on default passwords.”
Just in circumstance, while, Verifone mentioned vendors are “strongly suggested to modify the default password.” And currently, new Verifone equipment come with a password that expires.
In any circumstance, the fault lies with retailers and their particular suppliers. It can be like residence Wi-Fi. If you get a residence Wi-Fi router, it can be up to you to change the default passcode. Stores must be securing their have machines. And equipment resellers ought to be helping them do it.
Trustwave, which can help guard shops from hackers, mentioned that preserving credit rating card machines harmless is minimal on a store’s checklist of priorities.
“Businesses expend extra dollars choosing the coloration of the issue-of-sale than securing it,” Henderson claimed.
This trouble reinforces the conclusion built in a recent Verizon cybersecurity report: that merchants get hacked mainly because they’re lazy.
The default password detail is a critical difficulty. Retail pc networks get uncovered to personal computer viruses all the time. Look at one case Henderson investigated not too long ago. A terrible keystroke-logging spy program ended up on the computer a keep takes advantage of to course of action credit score card transactions. It turns out staff had rigged it to engage in a pirated variation of Guitar Hero, and accidentally downloaded the malware.
“It exhibits you the degree of accessibility that a lot of persons have to the issue-of-sale ecosystem,” he claimed. “Frankly, it is really not as locked down as it ought to be.”
CNNMoney (San Francisco) 1st printed April 29, 2015: 9:07 AM ET


More Stories
Car Stereo System and Its Installation
Black and Silver Nokia 6303 – Two Classic Models From the Nokia Camp
Motorcycle Clubs 101 – How to Create Motorcycle Club Bylaws Part I